Microsoft 70-680 Exam Practice Questions (P. 2)
- Full Access (551 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
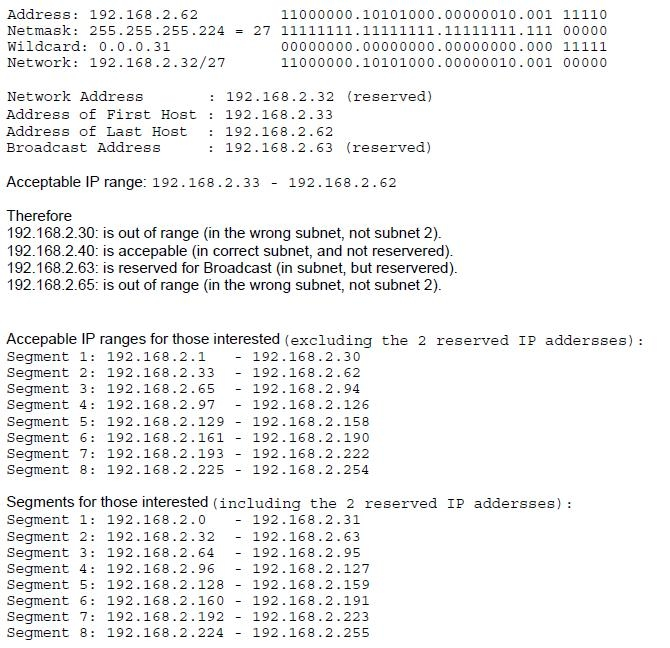
Question #11
Your company has a main office and a branch office. The relevant portion of the network is configured as shown in the exhibit. (Click the Exhibit button.)
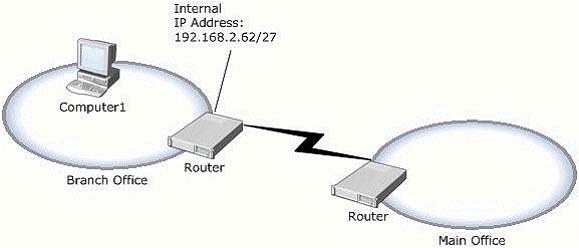
In the branch office, you deploy a new computer named Computer1 that runs Windows 7.
You need to assign an IP address to Computer1.
Which IP address should you use?
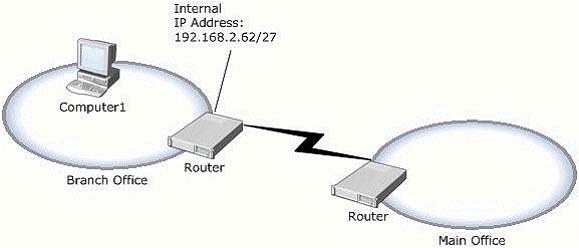
In the branch office, you deploy a new computer named Computer1 that runs Windows 7.
You need to assign an IP address to Computer1.
Which IP address should you use?
- A192.168.2.30
- B192.168.2.40
- C192.168.2.63
- D192.168.2.65
Correct Answer:
B
Internal IP Adress of router is 192.168.2.62/27Leaves 5 bits for range = 32 addresses (including the 2 reserved addresses)Subnet Mask = 255.255.255.224
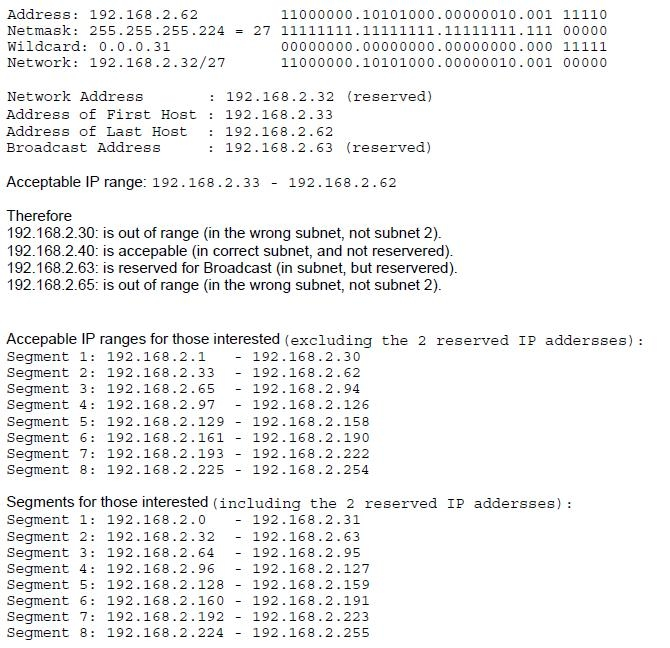
B
Internal IP Adress of router is 192.168.2.62/27Leaves 5 bits for range = 32 addresses (including the 2 reserved addresses)Subnet Mask = 255.255.255.224
send
light_mode
delete
Question #12
You work in an international company which is named Wiikigo. Before entering this company, you have two years of experience in the IT field, as well as experience implementing and administering any Windows client operating system in a networked environment. You are professional in installing, upgrading and migrating to Windows 7, deploying Windows 7, and configuring Hardware and Applications and son on. You are in charge of a computer that runs Windows Vista.
You have Windows 7 installed on a new partition on the computer. You have to make sure that the computer always starts Windows Vista by default. So what action should you perform to make sure of this?
You have Windows 7 installed on a new partition on the computer. You have to make sure that the computer always starts Windows Vista by default. So what action should you perform to make sure of this?
- AIn order to make sure that the computer always starts Windows Vista by default, a boot.ini file should be created in the root of the Windows 7 partition.
- BIn order to make sure that the computer always starts Windows Vista by default, a boot.ini file should be created in the root of the Windows Vista partition.
- CIn order to make sure that the computer always starts Windows Vista by default, Bcdedit.exe should be run and the /default parameter should be specified.
- DIn order to make sure that the computer always starts Windows Vista by default, Bcdedit.exe should be run and the /bootems parameter should be specified.
Correct Answer:
C
C
send
light_mode
delete
Question #13
You have a computer that runs Windows 7.
You run Ipconfig as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that you can establish a Direct Access connection to the network.
What should you do first?
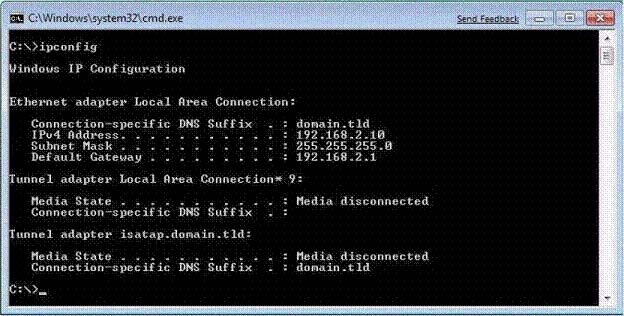
You run Ipconfig as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that you can establish a Direct Access connection to the network.
What should you do first?
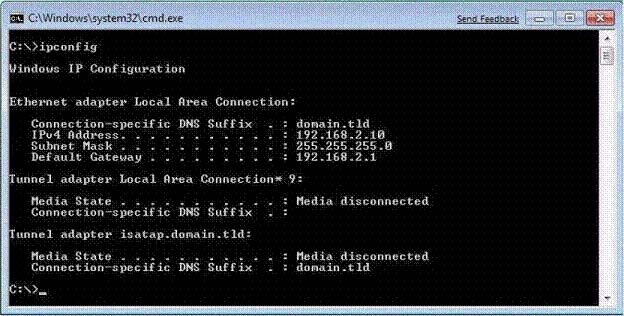
- ACreate a new VPN connection.
- BConfigure a static IPv4 address.
- CEnable IPv6 on the network adapter.
- DAdd an additional default gateway address.
Correct Answer:
C
C
send
light_mode
delete
Question #14
You have a computer that runs Windows Vista. The computer contains a custom application.
You need to export the user state and the settings of the custom application.
What should you do?
You need to export the user state and the settings of the custom application.
What should you do?
- ARun Loadstate.exe and specify the /config parameter.
- BRun Scanstate.exe and specify the /genconfig parameter.
- CModify the miguser.xml file. Run Loadstate.exe and specify the /ui parameter.
- DModify the migapp.xml file. Run Scanstate.exe and specify the /i parameter.
Correct Answer:
D
MigApp.xml This file contains rules about migrating application settings. These include Accessibility settings, dial-up connections, favorites, folder options, fonts, group membership, Open Database Connectivity (ODBC) settings, Microsoft Office Outlook Express mailbox files, mouse and keyboard settings, phone and modem options, Remote Access Service (RAS) connection phone book files, regional options, remote access, screensaver settings, taskbar settings, and wallpaper settings.
(Include) /i:[Path\]FileName
Specifies an .xml file that contains rules that define what user, application or system state to migrate. You can specify this option multiple times to include all of your .xml files (MigApp.xml, MigUser.xml and any custom .xml files that you create). Path can be either a relative or full path. If you do not specify the Path variable, then FileName must be located in the current directory.
D
MigApp.xml This file contains rules about migrating application settings. These include Accessibility settings, dial-up connections, favorites, folder options, fonts, group membership, Open Database Connectivity (ODBC) settings, Microsoft Office Outlook Express mailbox files, mouse and keyboard settings, phone and modem options, Remote Access Service (RAS) connection phone book files, regional options, remote access, screensaver settings, taskbar settings, and wallpaper settings.
(Include) /i:[Path\]FileName
Specifies an .xml file that contains rules that define what user, application or system state to migrate. You can specify this option multiple times to include all of your .xml files (MigApp.xml, MigUser.xml and any custom .xml files that you create). Path can be either a relative or full path. If you do not specify the Path variable, then FileName must be located in the current directory.
send
light_mode
delete
Question #15
You have a computer that runs Windows 7.
Multiple users log on to your computer.
You enable auditing on a folder stored on your computer.
You need to ensure that each access to the folder is logged.
What should you do?
Multiple users log on to your computer.
You enable auditing on a folder stored on your computer.
You need to ensure that each access to the folder is logged.
What should you do?
- AStart the Problem Steps Recorder.
- BFrom Event Viewer, modify the properties of the Security log.
- CFrom the local Group Policy, configure the Audit object access setting.
- DFrom the local Group Policy, configure the Audit directory service Access setting.
Correct Answer:
C
Audit object access -
Determines whether to audit the event of a user accessing an object (for example, file, folder, registry key, printer, and so forth) which has its own system access control list (SACL) specified. By default, this value is set to No auditing in the Default Domain Controller Group Policy object (GPO) and in the local policies of workstations and servers. If you define this policy setting, you can specify whether to audit successes, audit failures, or not to audit the event type at all. Success audits generate an audit entry when a user successfully accesses an object that has a SACL specified. Failure audits generate an audit entry when a user unsuccessfully attempts to access an object that has a SACL specified. You can select No auditing by defining the policy setting and unchecking Success and
Failure.
C
Audit object access -
Determines whether to audit the event of a user accessing an object (for example, file, folder, registry key, printer, and so forth) which has its own system access control list (SACL) specified. By default, this value is set to No auditing in the Default Domain Controller Group Policy object (GPO) and in the local policies of workstations and servers. If you define this policy setting, you can specify whether to audit successes, audit failures, or not to audit the event type at all. Success audits generate an audit entry when a user successfully accesses an object that has a SACL specified. Failure audits generate an audit entry when a user unsuccessfully attempts to access an object that has a SACL specified. You can select No auditing by defining the policy setting and unchecking Success and
Failure.
send
light_mode
delete
Question #16
You have a computer that runs Windows 7.
You discover that an application named App1 runs during the startup process.
You need to prevent only App1 from running during startup. Users must be allowed to run App1 manually.
What should you do?
You discover that an application named App1 runs during the startup process.
You need to prevent only App1 from running during startup. Users must be allowed to run App1 manually.
What should you do?
- AFrom the local Group Policy, modify the application control policy.
- BFrom the local Group Policy, modify the software restriction policy.
- CFrom the System Configuration tool, select Diagnostic Startup.
- DFrom the System Configuration tool, modify the Startup applications.
Correct Answer:
D
D
send
light_mode
delete
Question #17
You have a computer that runs Windows 7. The computer has two volumes named volume C and volume D.
You create a document on volume D.
You manually create a restore point and modify the document.
You view the properties of the document as shown in the exhibit. (Click the Exhibit button.)
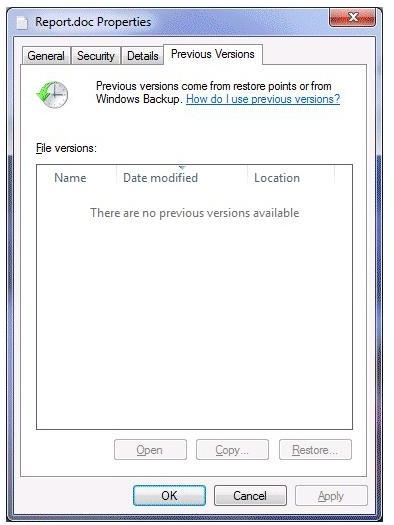
You need to ensure that you can restore the current version of the document if the document is modified.
What should you do first?
You create a document on volume D.
You manually create a restore point and modify the document.
You view the properties of the document as shown in the exhibit. (Click the Exhibit button.)
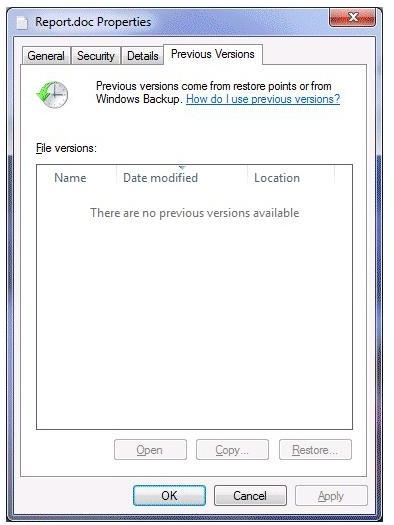
You need to ensure that you can restore the current version of the document if the document is modified.
What should you do first?
- ARun Disk Cleanup on volume D.
- BEnable auditing on the document.
- CTurn on System Protection for volume D.
- DStart the Volume Shadow Copy Service (VSS).
Correct Answer:
C
System Protection -
System protection regularly creates and saves information about your computers system files and settings. It also saves previous versions of files that you have modified. It saves these files in restore points, which are created just before significant system events, such as the installation of a program or device driver.
Restore points are also created automatically every seven days if no other restore points were created in the previous seven days. You can create restore points manually at any time. System protection is automatically on for the drive that holds the operating system and can be enabled only for drives that are formatted using the NTFS file system. It enables you to use system restore and to restore files to previous versions. You will configure system protection, create a restore point, and perform a system restore in the practice later in this lesson.
C
System Protection -
System protection regularly creates and saves information about your computers system files and settings. It also saves previous versions of files that you have modified. It saves these files in restore points, which are created just before significant system events, such as the installation of a program or device driver.
Restore points are also created automatically every seven days if no other restore points were created in the previous seven days. You can create restore points manually at any time. System protection is automatically on for the drive that holds the operating system and can be enabled only for drives that are formatted using the NTFS file system. It enables you to use system restore and to restore files to previous versions. You will configure system protection, create a restore point, and perform a system restore in the practice later in this lesson.
send
light_mode
delete
Question #18
You start a computer by using Windows Preinstallation Environment (Windows PE).
You need to dynamically load a network adapter device driver in Windows PE.
What should you do?
You need to dynamically load a network adapter device driver in Windows PE.
What should you do?
- ARun Peimg.exe and specify the device driver path.
- BRun Drvload.exe and specify the device driver path.
- CRun Winpeshl.exe and specify a custom Winpeshl.ini file.
- DRun Wpeutil.exe and specify the Initialize Network command.
Correct Answer:
B
The Drvload tool adds out-of-box drivers to a booted Windows PE image. It takes one or more driver .inf files as inputs. To add a driver to an offline Windows PE image, use the peimg tool.
B
The Drvload tool adds out-of-box drivers to a booted Windows PE image. It takes one or more driver .inf files as inputs. To add a driver to an offline Windows PE image, use the peimg tool.
send
light_mode
delete
Question #19
Your company has an Active Directory domain. All computers are members of the domain.
Your network contains an internal Web site that uses Integrated Windows Authentication.
From a computer that runs Windows 7, you attempt to connect to the Web site and are prompted for authentication.
You verify that your user account has permission to access the Web site.
You need to ensure that you are automatically authenticated when you connect to the Web site.
What should you do?
Your network contains an internal Web site that uses Integrated Windows Authentication.
From a computer that runs Windows 7, you attempt to connect to the Web site and are prompted for authentication.
You verify that your user account has permission to access the Web site.
You need to ensure that you are automatically authenticated when you connect to the Web site.
What should you do?
- ACreate a complex password for your user account.
- BOpen Credential Manager and modify your credentials.
- CAdd the URL of the Web site to the Trusted sites zone.
- DAdd the URL of the Web site to the Local intranet zone.
Correct Answer:
D
Local Intranet Sites in the Local Intranet zone are computers on your organizational intranet. Internet Explorer can be configured to detect intranet sites automatically. It is also possible to add Web sites to this zone by clicking the Advanced button on the Local Intranet sites dialog box, as shown in the figure. The default security level of this zone is Medium-Low. Protected Mode is not enabled by default for sites in this zone.
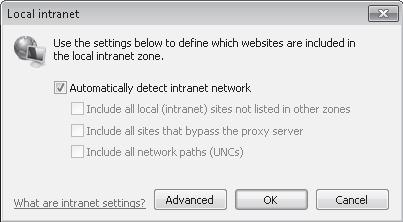
Security settings are configured primarily by assigning sites to zones. Sites that require elevated privileges should be assigned to the Trusted Sites zone. Sites that are on the intranet are automatically assigned to the Local Intranet zone, though this may require manual configuration in some circumstances. All other sites are assigned to the Internet zone. The Restricted Sites zone is used only for Web sites that may present security risks but must be visited.
D
Local Intranet Sites in the Local Intranet zone are computers on your organizational intranet. Internet Explorer can be configured to detect intranet sites automatically. It is also possible to add Web sites to this zone by clicking the Advanced button on the Local Intranet sites dialog box, as shown in the figure. The default security level of this zone is Medium-Low. Protected Mode is not enabled by default for sites in this zone.
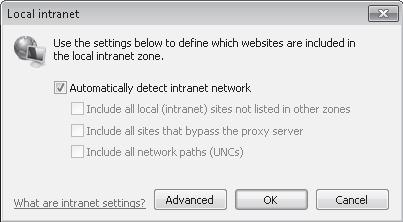
Security settings are configured primarily by assigning sites to zones. Sites that require elevated privileges should be assigned to the Trusted Sites zone. Sites that are on the intranet are automatically assigned to the Local Intranet zone, though this may require manual configuration in some circumstances. All other sites are assigned to the Internet zone. The Restricted Sites zone is used only for Web sites that may present security risks but must be visited.
send
light_mode
delete
Question #20
Your network contains a wireless access point. You have a computer that runs Windows 7. The computer connects to the wireless access point.
You disable Service Set Identifier (SSID) broadcasts on the wireless access point.
You discover that you are now unable to connect to the wireless access point from the Windows 7 computer.
You need to ensure that the computer can connect to the wireless access point.
What should you do?
You disable Service Set Identifier (SSID) broadcasts on the wireless access point.
You discover that you are now unable to connect to the wireless access point from the Windows 7 computer.
You need to ensure that the computer can connect to the wireless access point.
What should you do?
- AFrom Credential Manager, modify the generic credentials.
- BFrom Credential Manager, modify the Windows credentials.
- CFrom Network and Sharing Center, turn on Network discovery.
- DFrom Network and Sharing Center, modify the wireless network connection settings.
Correct Answer:
D
Wireless Network Connection settings
To connect to a wireless network that does not broadcast its SSID, you need to know details such as the network name and security type. In Network And Sharing
Center, you click Set UpA Connection Or Network, click Manually Connect To A Wireless Network, and click Next. You are prompted for the network name and security type and (if appropriate) encryption type and security key. Alternatively, you can open an elevated command prompt and enter a command with the following syntax: netsh wlan connect name=<profile_name> ssid-<network_ssid> [interface=<interface_name>] (Since the computer has previously been connected, just modify the settings.)
D
Wireless Network Connection settings
To connect to a wireless network that does not broadcast its SSID, you need to know details such as the network name and security type. In Network And Sharing
Center, you click Set UpA Connection Or Network, click Manually Connect To A Wireless Network, and click Next. You are prompted for the network name and security type and (if appropriate) encryption type and security key. Alternatively, you can open an elevated command prompt and enter a command with the following syntax: netsh wlan connect name=<profile_name> ssid-<network_ssid> [interface=<interface_name>] (Since the computer has previously been connected, just modify the settings.)
send
light_mode
delete
All Pages
