CompTIA CS0-001 Exam Practice Questions (P. 1)
- Full Access (416 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
Question #1
SIMULATION -
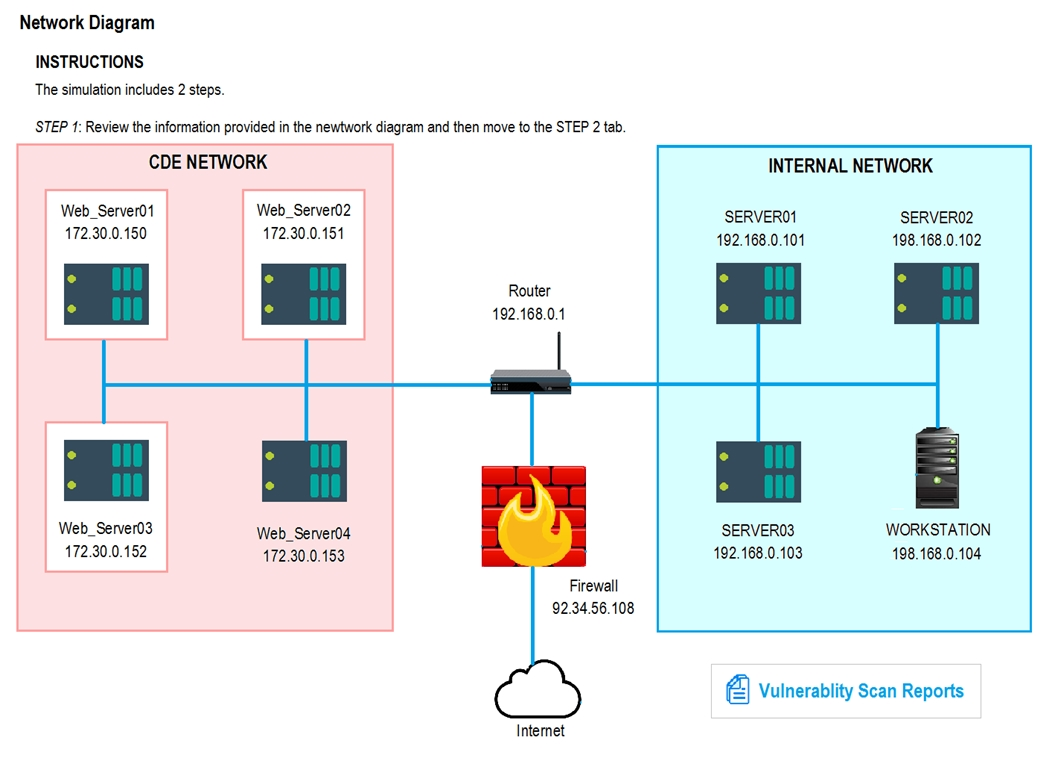
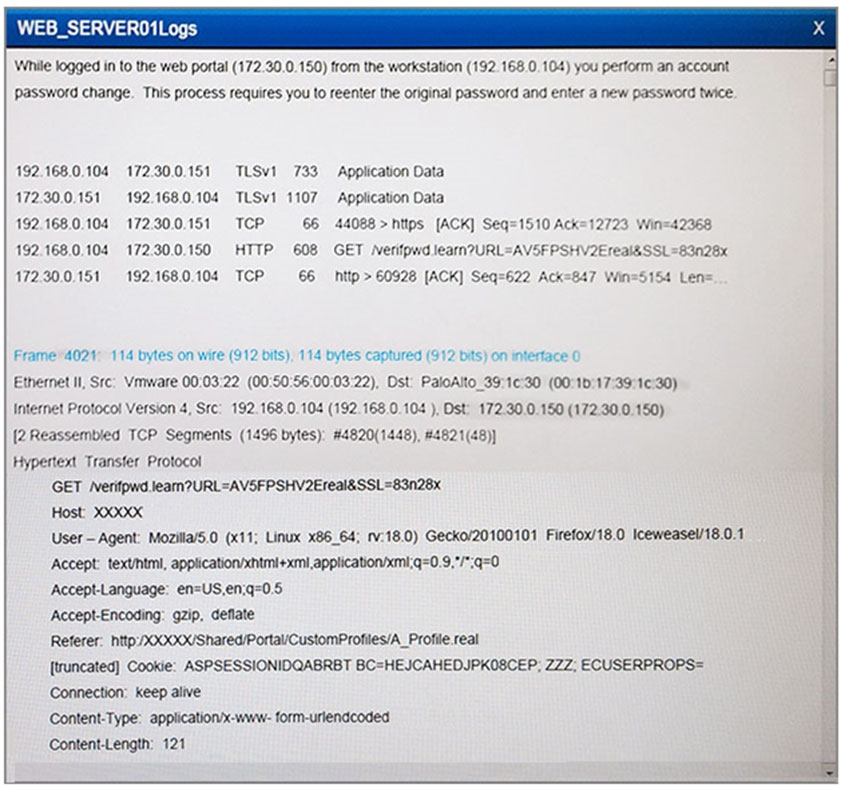
The developers recently deployed new code to three web servers. A daily automated external device scan report shows server vulnerabilities that are failing items according to PCI DSS.
If the vulnerability is not valid, the analyst must take the proper steps to get the scan clean.
If the vulnerability is valid, the analyst must remediate the finding.
After reviewing the information provided in the network diagram, select the STEP 2 tab to complete the simulation by selecting the correct Validation Result and
Remediation Action for each server listed using the drop-down options.
Instructions -
STEP 1: Review the information provided in the network diagram.
STEP 2: Given the scenario, determine which remediation action is required to address the vulnerability.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
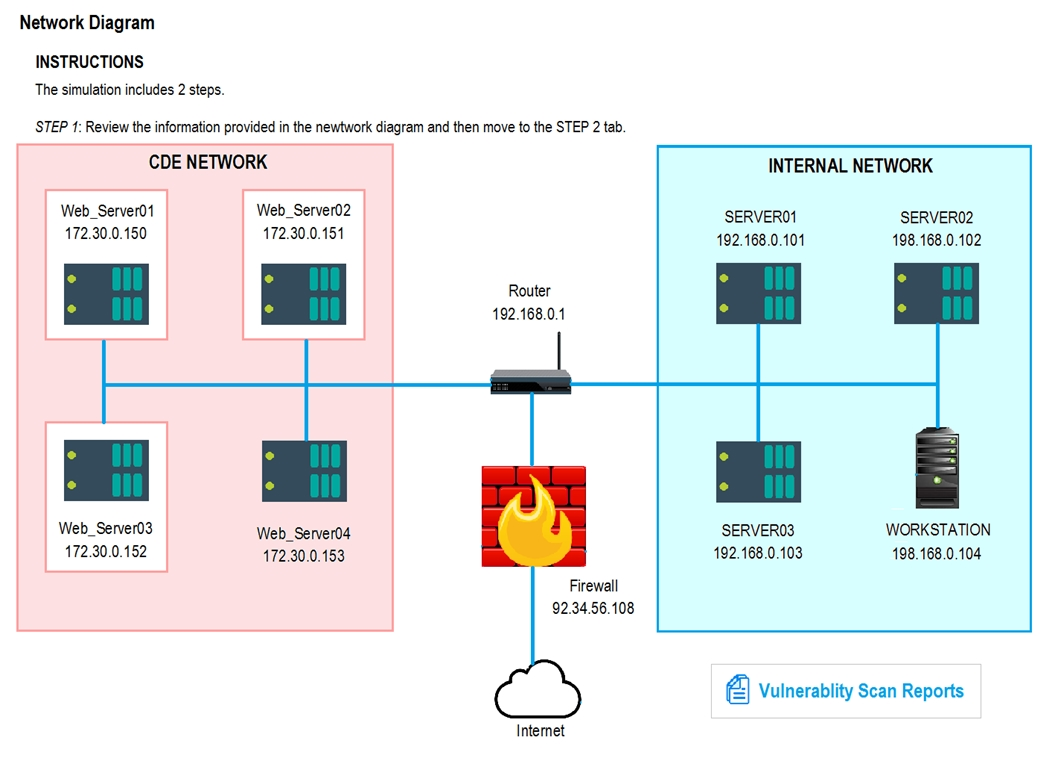
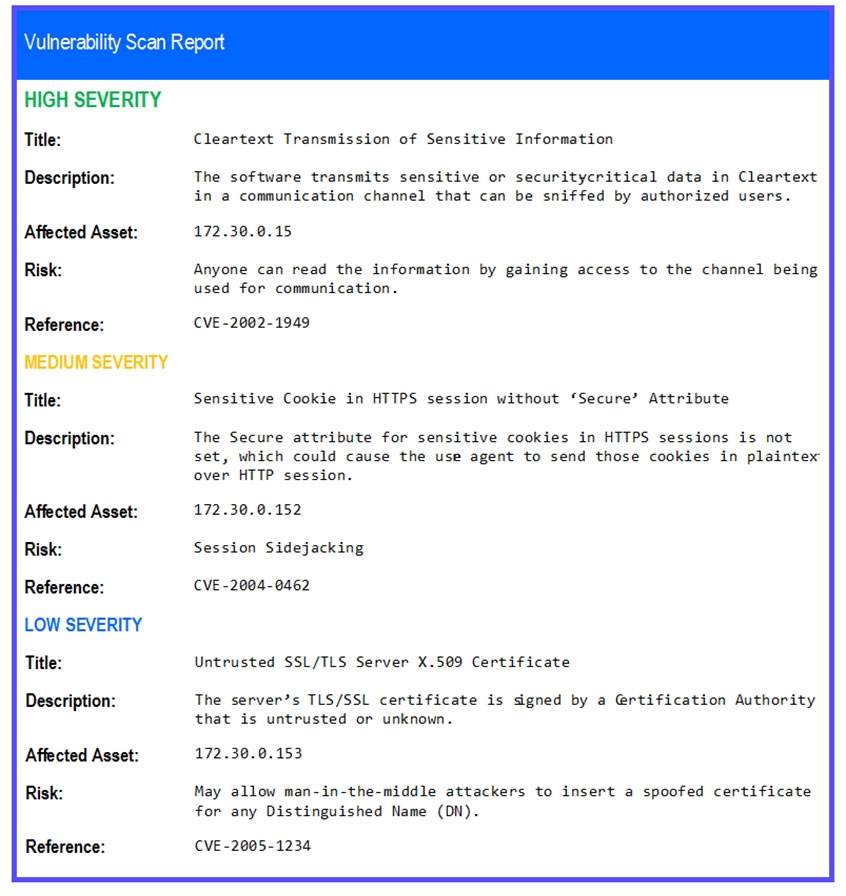
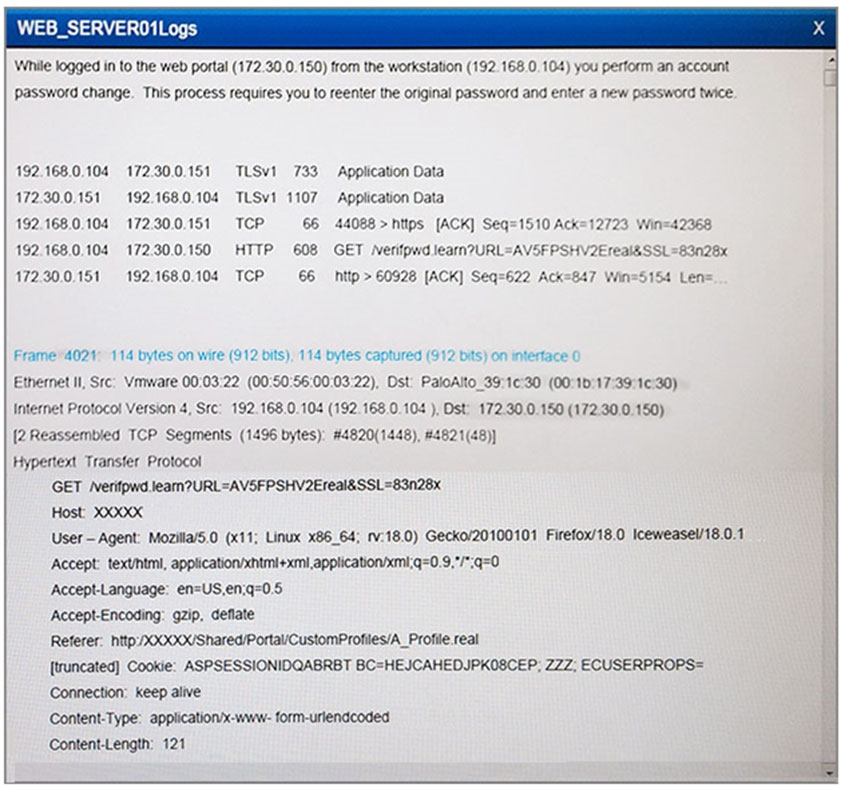
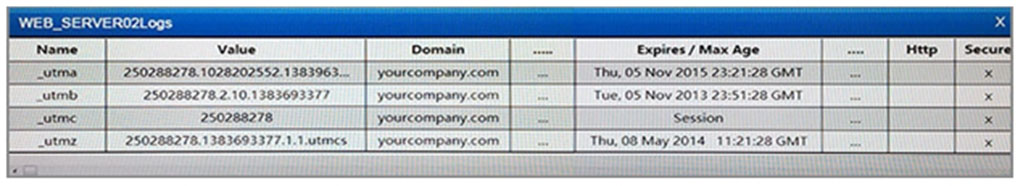
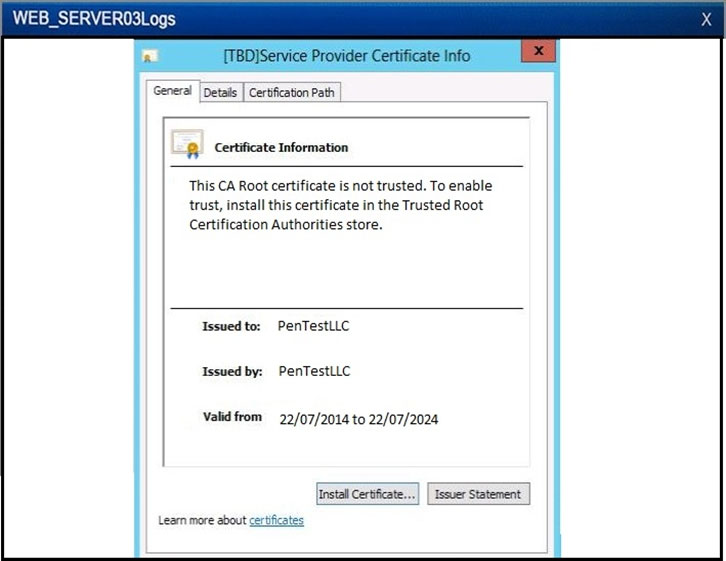
The developers recently deployed new code to three web servers. A daily automated external device scan report shows server vulnerabilities that are failing items according to PCI DSS.
If the vulnerability is not valid, the analyst must take the proper steps to get the scan clean.
If the vulnerability is valid, the analyst must remediate the finding.
After reviewing the information provided in the network diagram, select the STEP 2 tab to complete the simulation by selecting the correct Validation Result and
Remediation Action for each server listed using the drop-down options.
Instructions -
STEP 1: Review the information provided in the network diagram.
STEP 2: Given the scenario, determine which remediation action is required to address the vulnerability.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
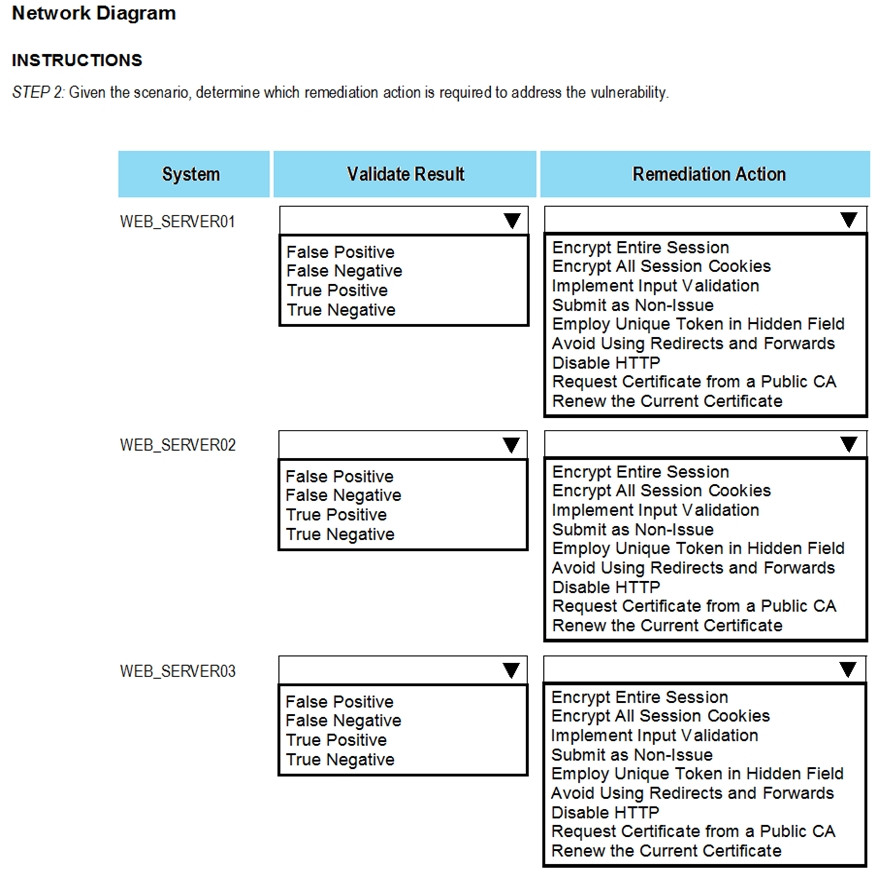
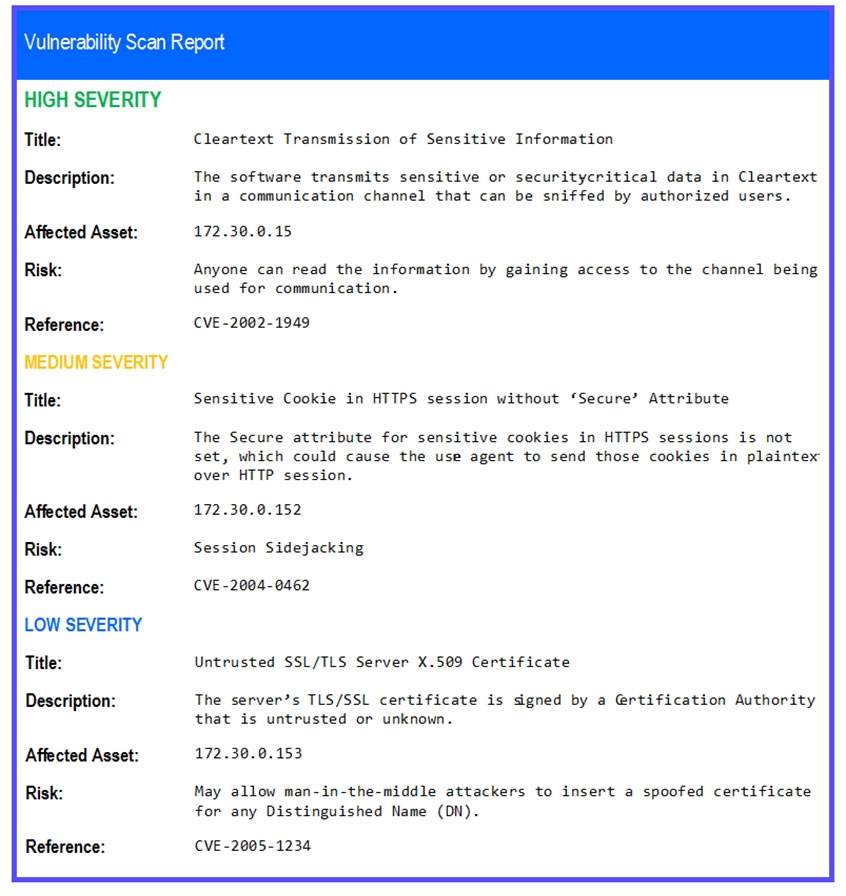
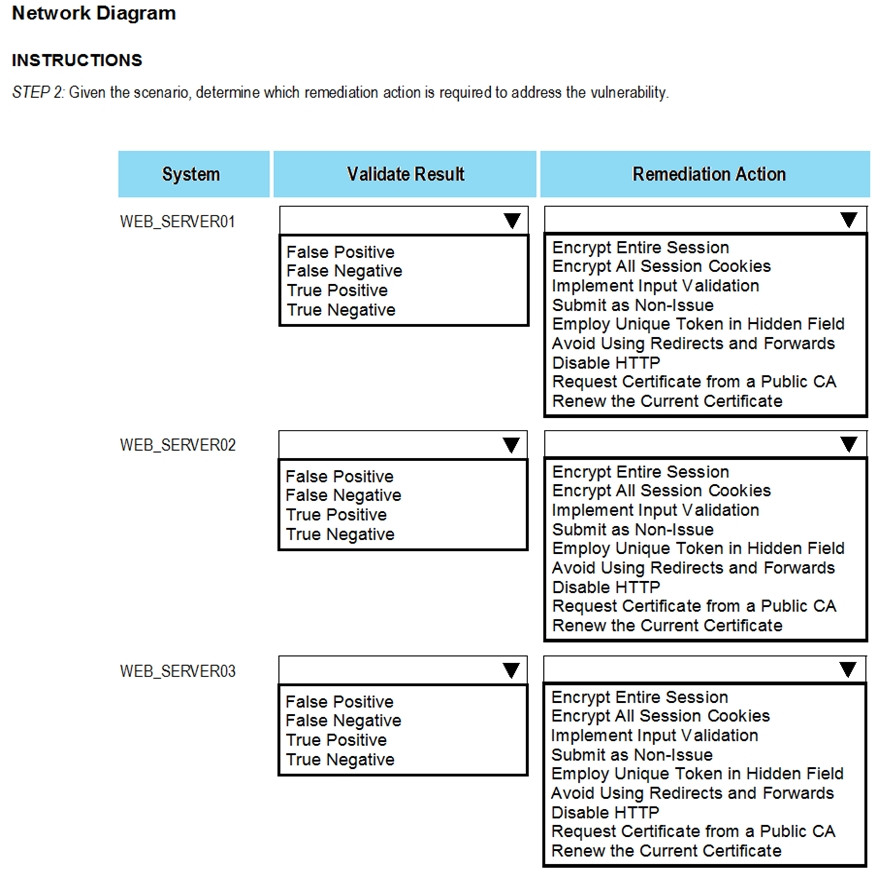
Correct Answer:
See the answer below
WEB_SERVER01: VALID "" IMPLEMENT SSL/TLS
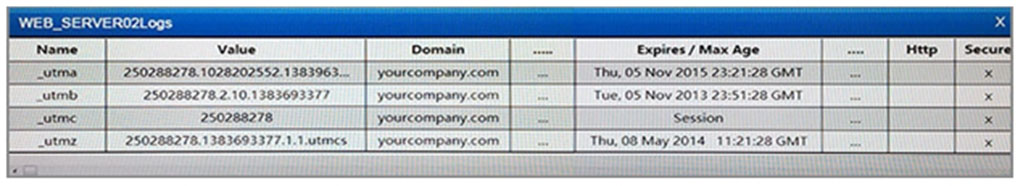
WEB_SERVER02: VALID "" SET SECURE ATTRIBUTE WHEN COOKIE SHOULD SENT VIA HTTPS ONLY
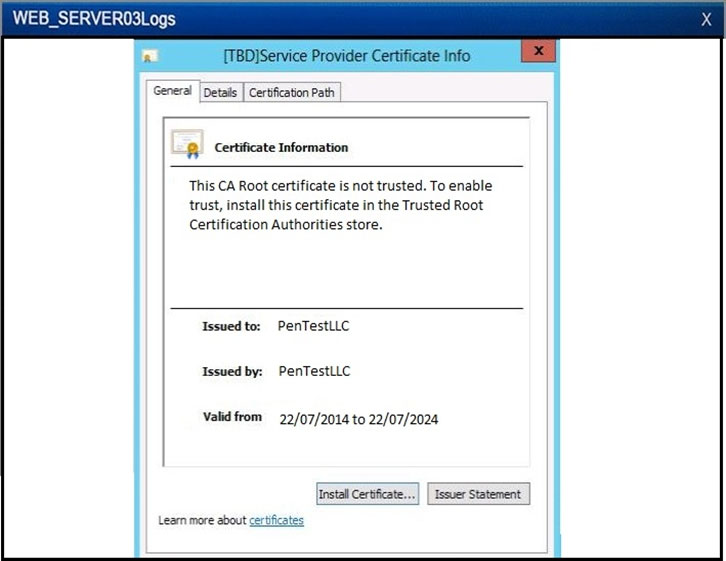
WEB_SERVER03: VALID "" IMPLEMENT CA SIGNED CERTIFICATE
See the answer below
WEB_SERVER01: VALID "" IMPLEMENT SSL/TLS
WEB_SERVER02: VALID "" SET SECURE ATTRIBUTE WHEN COOKIE SHOULD SENT VIA HTTPS ONLY
WEB_SERVER03: VALID "" IMPLEMENT CA SIGNED CERTIFICATE
send
light_mode
delete
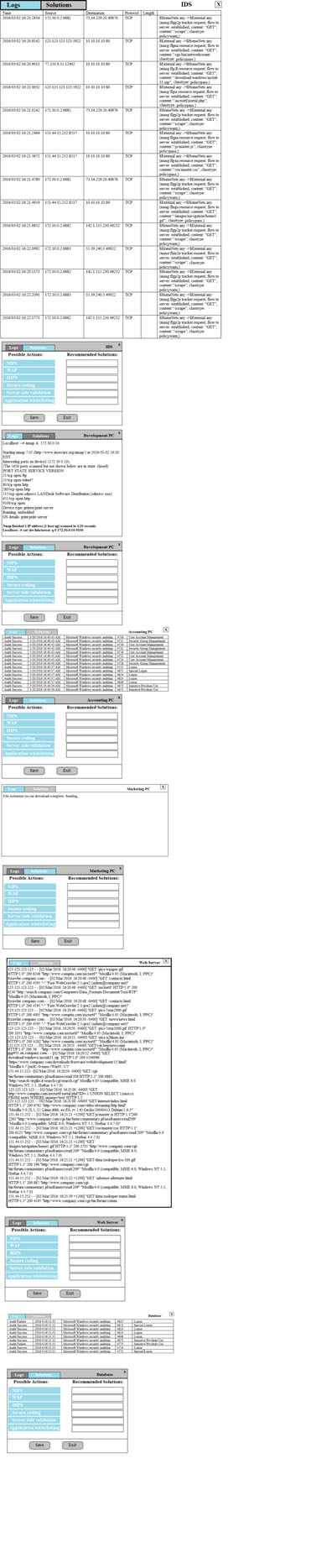
Question #2
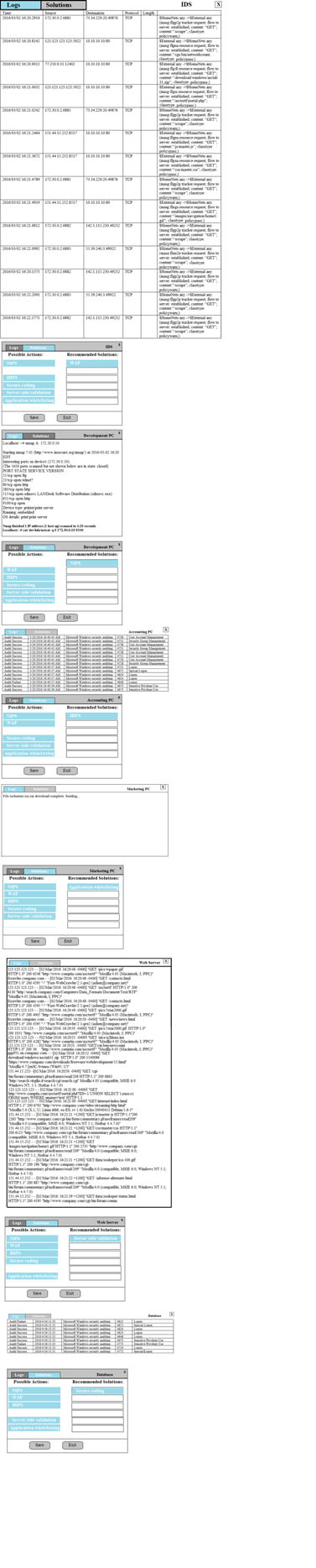
DRAG DROP -
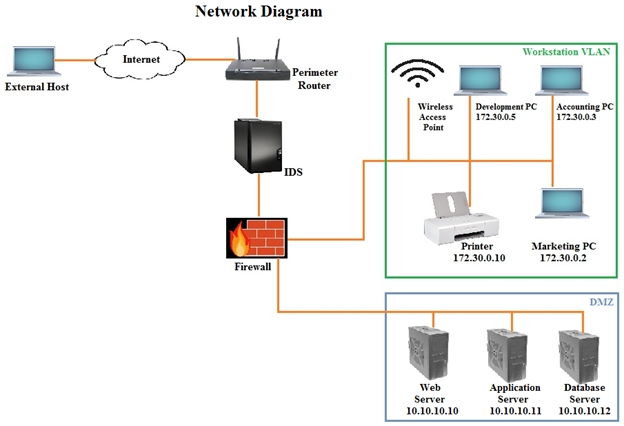
You suspect that multiple unrelated security events have occurred on several nodes on a corporate network. You must review all logs and correlate events when necessary to discover each security event by clicking on each node. Only select corrective actions if the logs shown a security event that needs remediation. Drag and drop the appropriate corrective actions to mitigate the specific security event occurring on each affected device.
Instructions:
The Web Server, Database Server, IDS, Development PC, Accounting PC and Marketing PC are clickable. Some actions may not be required and each actions can only be used once per node. The corrective action order is not important. If at any time you would like to bring back the initial state of the simulation, please select the Reset button. When you have completed the simulation, please select the Done button to submit. Once the simulation is submitted, please select the
Next button to continue.
Select and Place:
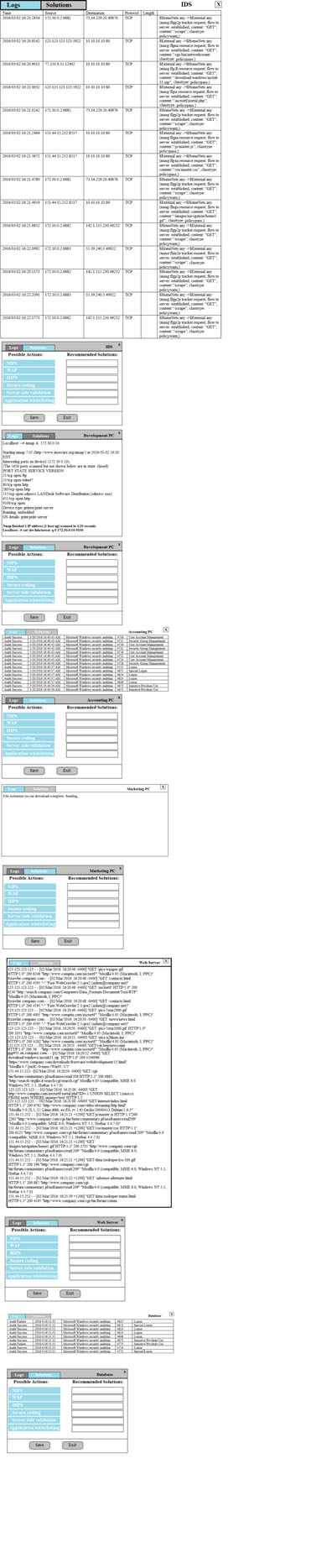
You suspect that multiple unrelated security events have occurred on several nodes on a corporate network. You must review all logs and correlate events when necessary to discover each security event by clicking on each node. Only select corrective actions if the logs shown a security event that needs remediation. Drag and drop the appropriate corrective actions to mitigate the specific security event occurring on each affected device.
Instructions:
The Web Server, Database Server, IDS, Development PC, Accounting PC and Marketing PC are clickable. Some actions may not be required and each actions can only be used once per node. The corrective action order is not important. If at any time you would like to bring back the initial state of the simulation, please select the Reset button. When you have completed the simulation, please select the Done button to submit. Once the simulation is submitted, please select the
Next button to continue.
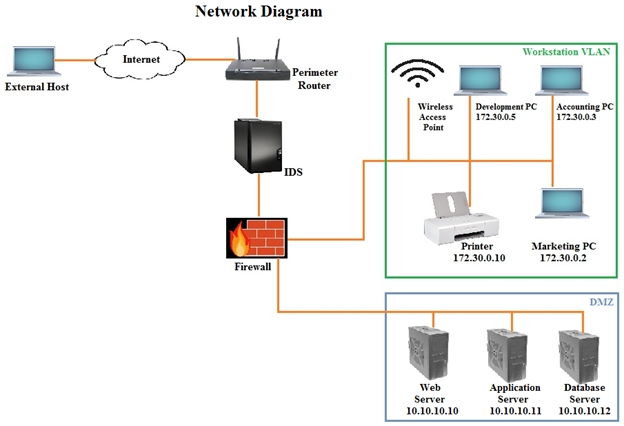
Select and Place:
send
light_mode
delete
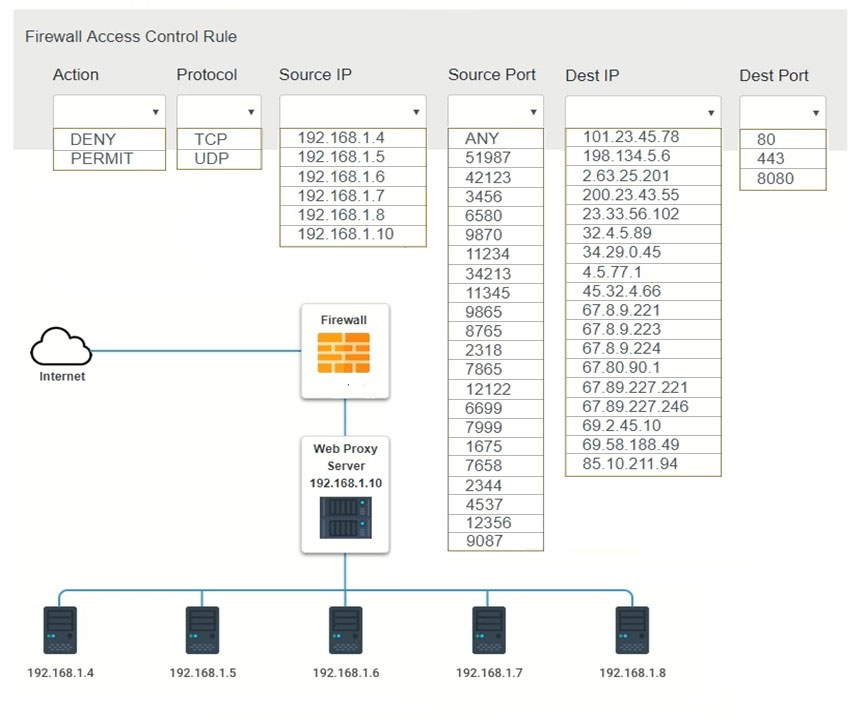
Question #3
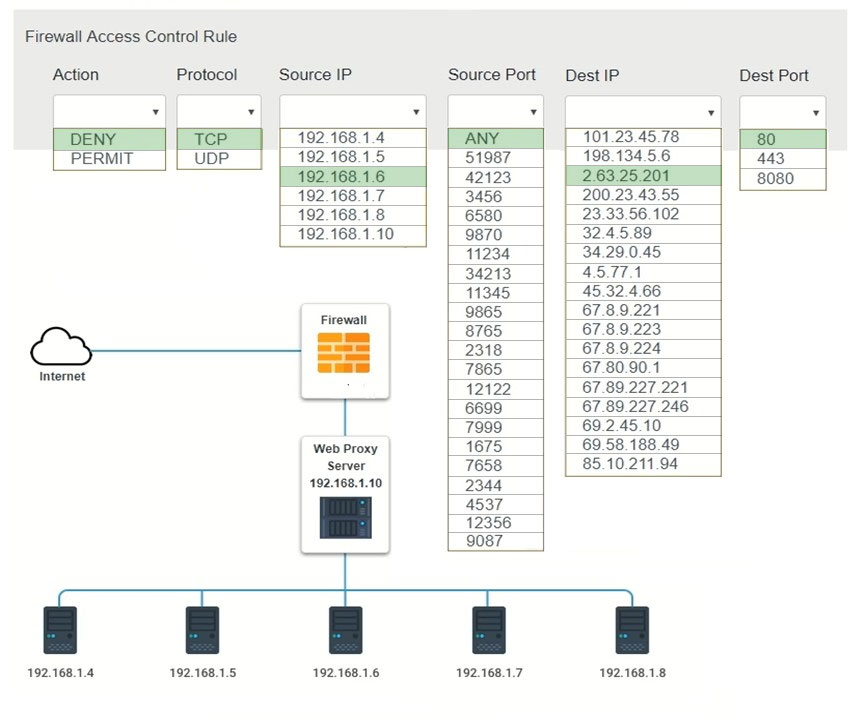
HOTSPOT -
A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company's web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization.
Instructions:
Modify the firewall ACL, using the Firewall ACL form to mitigate the issue.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
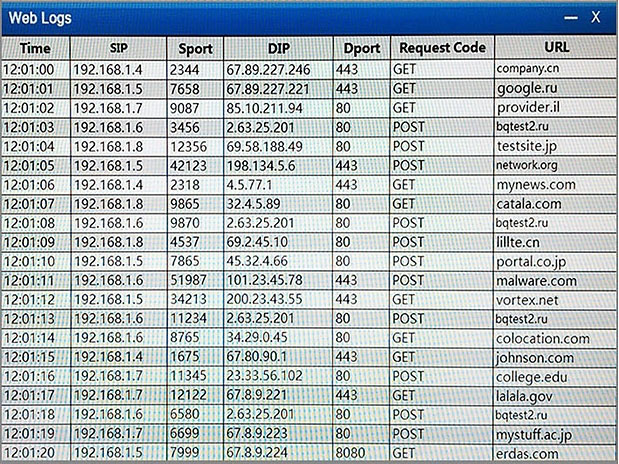
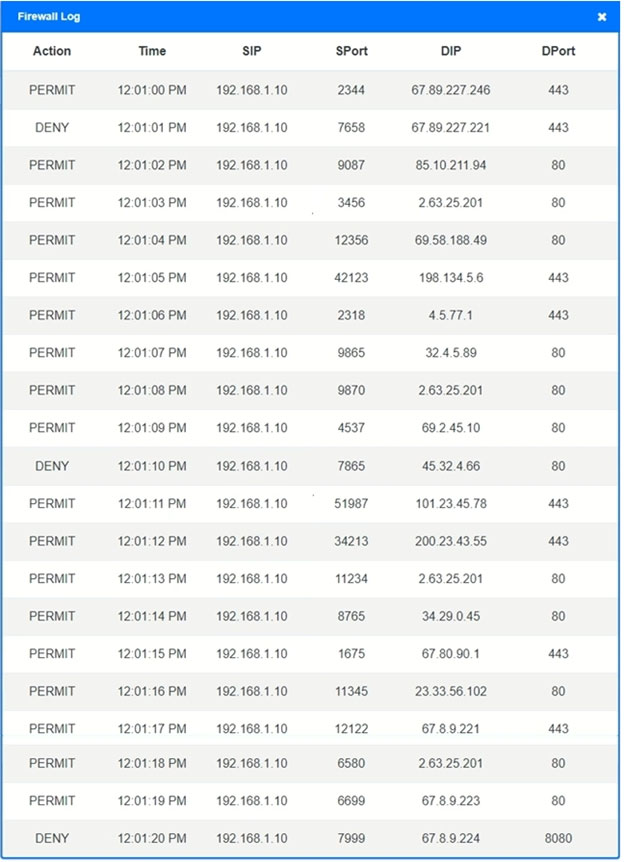
Hot Area:
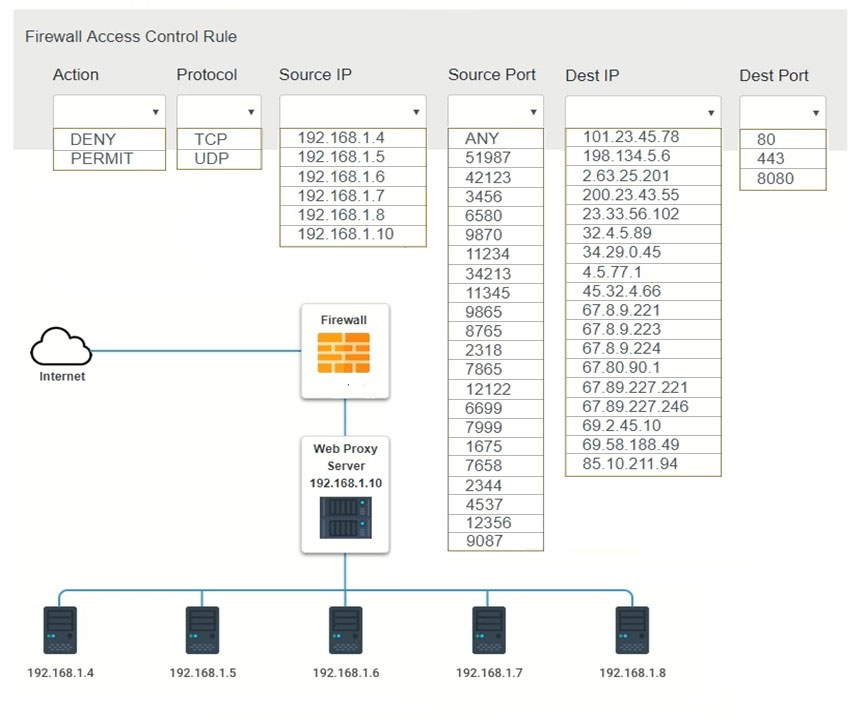
A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company's web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization.
Instructions:
Modify the firewall ACL, using the Firewall ACL form to mitigate the issue.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
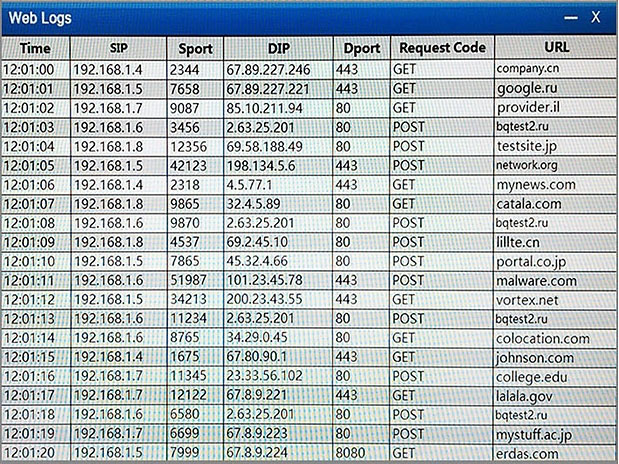
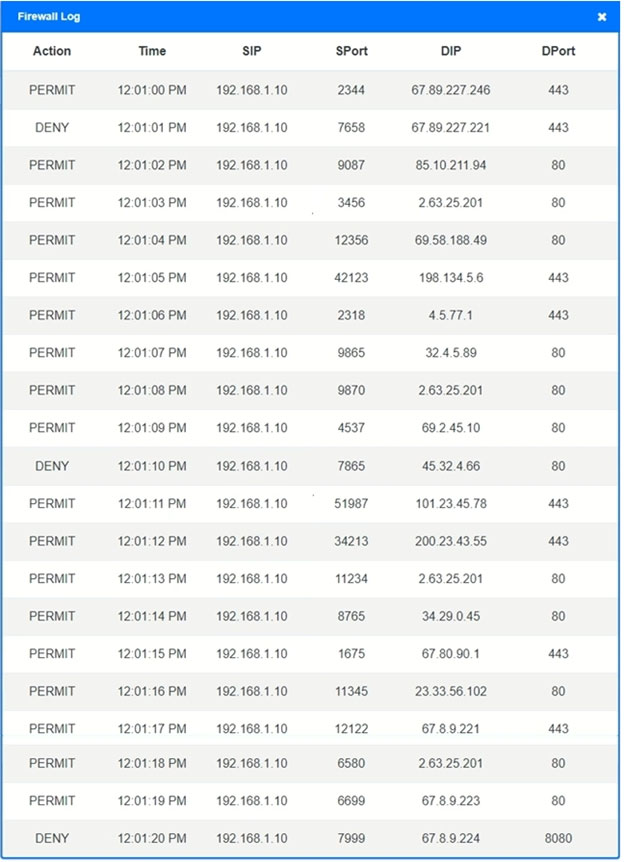
Hot Area:
send
light_mode
delete
Question #4
Which of the following BEST describes the offensive participants in a tabletop exercise?
- ARed team
- BBlue team
- CSystem administrators
- DSecurity analysts
- EOperations team
Correct Answer:
A
A
send
light_mode
delete
Question #5
After analyzing and correlating activity from multiple sensors, the security analyst has determined a group from a high-risk country is responsible for a sophisticated breach of the company network and continuous administration of targeted attacks for the past three months. Until now, the attacks went unnoticed.
This is an example of:
This is an example of:
- Aprivilege escalation.
- Badvanced persistent threat.
- Cmalicious insider threat.
- Dspear phishing.
Correct Answer:
B
B
send
light_mode
delete
Question #6
A system administrator who was using an account with elevated privileges deleted a large amount of log files generated by a virtual hypervisor in order to free up disk space. These log files are needed by the security team to analyze the health of the virtual machines. Which of the following compensating controls would help prevent this from reoccurring? (Choose two.)
- ASuccession planning
- BSeparation of duties
- CMandatory vacation
- DPersonnel training
- EJob rotation
Correct Answer:
BD
BD
send
light_mode
delete
Question #7
Which of the following best practices is used to identify areas in the network that may be vulnerable to penetration testing from known external sources?
- ABlue team training exercises
- BTechnical control reviews
- CWhite team training exercises
- DOperational control reviews
Correct Answer:
A
A
send
light_mode
delete
Question #8
An organization has recently recovered from an incident where a managed switch had been accessed and reconfigured without authorization by an insider. The incident response team is working on developing a lessons learned report with recommendations. Which of the following recommendations will BEST prevent the same attack from occurring in the future?
- ARemove and replace the managed switch with an unmanaged one.
- BImplement a separate logical network segment for management interfaces.
- CInstall and configure NAC services to allow only authorized devices to connect to the network.
- DAnalyze normal behavior on the network and configure the IDS to alert on deviations from normal.
Correct Answer:
B
B
send
light_mode
delete
Question #9
A cybersecurity analyst is reviewing the current BYOD security posture. The users must be able to synchronize their calendars, email, and contacts to a smartphone or other personal device. The recommendation must provide the most flexibility to users. Which of the following recommendations would meet both the mobile data protection efforts and the business requirements described in this scenario?
- ADevelop a minimum security baseline while restricting the type of data that can be accessed.
- BImplement a single computer configured with USB access and monitored by sensors.
- CDeploy a kiosk for synchronizing while using an access list of approved users.
- DImplement a wireless network configured for mobile device access and monitored by sensors.
Correct Answer:
D
D
send
light_mode
delete
Question #10
A security analyst received a compromised workstation. The workstation's hard drive may contain evidence of criminal activities. Which of the following is the
FIRST thing the analyst must do to ensure the integrity of the hard drive while performing the analysis?
FIRST thing the analyst must do to ensure the integrity of the hard drive while performing the analysis?
- AMake a copy of the hard drive.
- BUse write blockers.
- CRun rm ""R command to create a hash.
- DInstall it on a different machine and explore the content.
Correct Answer:
B
B
send
light_mode
delete
All Pages