CompTIA SY0-501 Exam Practice Questions (P. 5)
- Full Access (1132 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
Question #41
A department head at a university resigned on the first day of the spring semester. It was subsequently determined that the department head deleted numerous files and directories from the server-based home directory while the campus was closed. Which of the following policies or procedures could have prevented this from occurring?
- ATime-of-day restrictions
- BPermission auditing and review
- COffboarding
- DAccount expiration
Correct Answer:
C
C
send
light_mode
delete
Question #42
A database backup schedule consists of weekly full backups performed on Saturday at 12:00 a.m. and daily differential backups also performed at 12:00 a.m. If the database is restored on Tuesday afternoon, which of the following is the number of individual backups that would need to be applied to complete the database recovery?
send
light_mode
delete
Question #43
Which of the following security controls does an iris scanner provide?
send
light_mode
delete
Question #44
As part of a new industry regulation, companies are required to utilize secure, standardized OS settings. A technical must ensure the OS settings are hardened.
Which of the following is the BEST way to do this?
Which of the following is the BEST way to do this?
- AUse a vulnerability scanner.
- BUse a configuration compliance scanner.
- CUse a passive, in-line scanner.
- DUse a protocol analyzer.
Correct Answer:
B
B
send
light_mode
delete
Question #45
A user has attempted to access data at a higher classification level than the user's account is currently authorized to access. Which of the following access control models has been applied to this user's account?
send
light_mode
delete
Question #46
A security consultant discovers that an organization is using the PCL protocol to print documents, utilizing the default driver and print settings. Which of the following is the MOST likely risk in this situation?
- AAn attacker can access and change the printer configuration.
- BSNMP data leaving the printer will not be properly encrypted.
- CAn MITM attack can reveal sensitive information.Most Voted
- DAn attacker can easily inject malicious code into the printer firmware.
- EAttackers can use the PCL protocol to bypass the firewall of client computers.
Correct Answer:
B
B
send
light_mode
delete
Question #47
An organization finds that most help desk calls are regarding account lockout due to a variety of applications running on different systems. Management is looking for a solution to reduce the number of account lockouts while improving security. Which of the following is the BEST solution for this organization?
- ACreate multiple application accounts for each user.
- BProvide secure tokens.
- CImplement SSO.
- DUtilize role-based access control.
Correct Answer:
C
C
send
light_mode
delete
Question #48
A user suspects someone has been accessing a home network without permission by spoofing the MAC address of an authorized system. While attempting to determine if an authorized user is logged into the home network, the user reviews the wireless router, which shows the following table for systems that are currently on the home network.
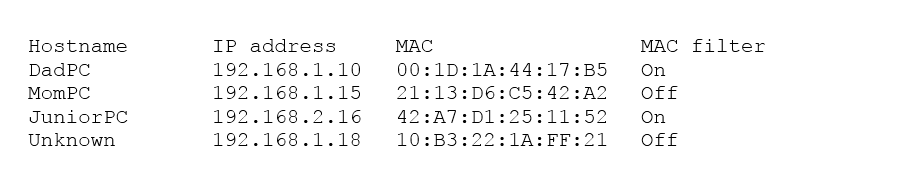
Which of the following should be the NEXT step to determine if there is an unauthorized user on the network?
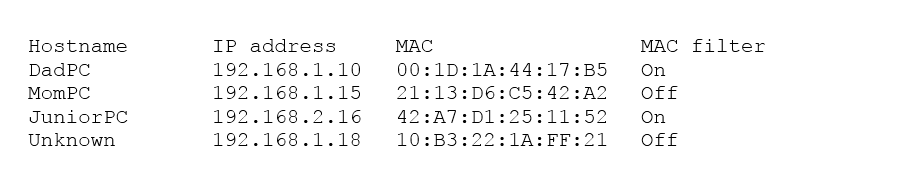
Which of the following should be the NEXT step to determine if there is an unauthorized user on the network?
- AApply MAC filtering and see if the router drops any of the systems.
- BPhysically check each of the authorized systems to determine if they are logged onto the network.
- CDeny the ג€unknownג€ host because the hostname is not known and MAC filtering is not applied to this host.
- DConduct a ping sweep of each of the authorized systems and see if an echo response is received.
Correct Answer:
B
B
send
light_mode
delete
Question #49
When performing data acquisition on a workstation, which of the following should be captured based on memory volatility? (Choose two.)
- AUSB-attached hard disk
- BSwap/pagefile
- CMounted network storage
- DROM
- ERAM
Correct Answer:
BE
BE
send
light_mode
delete
Question #50
Ann, a security administrator, has been instructed to perform fuzz-based testing on the company's applications.
Which of the following best describes what she will do?
Which of the following best describes what she will do?
- AEnter random or invalid data into the application in an attempt to cause it to fault
- BWork with the developers to eliminate horizontal privilege escalation opportunities
- CTest the applications for the existence of built-in- back doors left by the developers
- DHash the application to verify it won't cause a false positive on the HIPS
Correct Answer:
A
A
send
light_mode
delete
All Pages
