CompTIA SY0-501 Exam Practice Questions (P. 4)
- Full Access (1132 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
Question #31
When trying to log onto a company's new ticketing system, some employees receive the following message: Access denied: too many concurrent sessions. The ticketing system was recently installed on a small VM with only the recommended hardware specifications. Which of the following is the MOST likely cause for this error message?
- ANetwork resources have been exceeded.
- BThe software is out of licenses.
- CThe VM does not have enough processing power.
- DThe firewall is misconfigured.
Correct Answer:
C
C
send
light_mode
delete
Question #32
Joe, an employee, wants to show his colleagues how much he knows about smartphones. Joe demonstrates a free movie application that he installed from a third party on his corporate smartphone. Joe's colleagues were unable to find the application in the app stores. Which of the following allowed Joe to install the application? (Choose two.)
- ANear-field communication.
- BRooting/jailbreaking
- CAd-hoc connections
- DTethering
- ESideloading
Correct Answer:
BE
BE
send
light_mode
delete
Question #33
Which of the following can be provided to an AAA system for the identification phase?
send
light_mode
delete
Question #34
Which of the following implements two-factor authentication?
- AA phone system requiring a PIN to make a call
- BAt ATM requiring a credit card and PIN
- CA computer requiring username and password
- DA datacenter mantrap requiring fingerprint and iris scan
Correct Answer:
B
B
send
light_mode
delete
Question #35
Malicious traffic from an internal network has been detected on an unauthorized port on an application server.
Which of the following network-based security controls should the engineer consider implementing?
Which of the following network-based security controls should the engineer consider implementing?
send
light_mode
delete
Question #36
A network administrator wants to implement a method of securing internal routing. Which of the following should the administrator implement?
send
light_mode
delete
Question #37
A security administrator is developing controls for creating audit trails and tracking if a PHI data breach is to occur. The administrator has been given the following requirements:
All access must be correlated to a user account.

✑ All user accounts must be assigned to a single individual.
✑ User access to the PHI data must be recorded.
✑ Anomalies in PHI data access must be reported.
✑ Logs and records cannot be deleted or modified.
Which of the following should the administrator implement to meet the above requirements? (Choose three.)
All access must be correlated to a user account.

✑ All user accounts must be assigned to a single individual.
✑ User access to the PHI data must be recorded.
✑ Anomalies in PHI data access must be reported.
✑ Logs and records cannot be deleted or modified.
Which of the following should the administrator implement to meet the above requirements? (Choose three.)
- AEliminate shared accounts.
- BCreate a standard naming convention for accounts.
- CImplement usage auditing and review.
- DEnable account lockout thresholds.
- ECopy logs in real time to a secured WORM drive.
- FImplement time-of-day restrictions.
- GPerform regular permission audits and reviews.
Correct Answer:
ACE
ACE
send
light_mode
delete
Question #38
Which of the following encryption methods does PKI typically use to securely protect keys?
send
light_mode
delete
Question #39
An organization is using a tool to perform a source code review. Which of the following describes the case in which the tool incorrectly identifies the vulnerability?
send
light_mode
delete
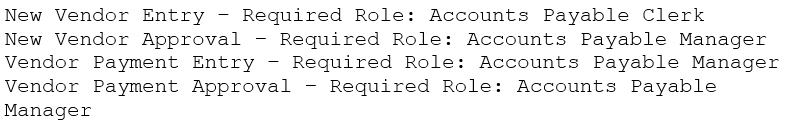
Question #40
An organization's internal auditor discovers that large sums of money have recently been paid to a vendor that management does not recognize. The IT security department is asked to investigate the organizations the organization's ERP system to determine how the accounts payable module has been used to make these vendor payments.
The IT security department finds the following security configuration for the accounts payable module:
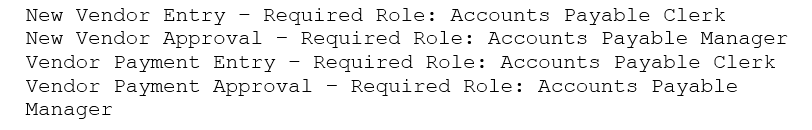
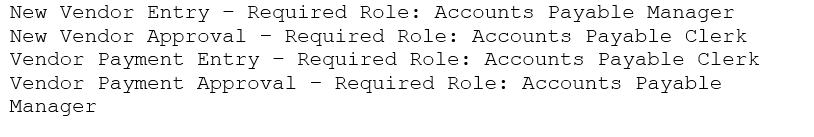
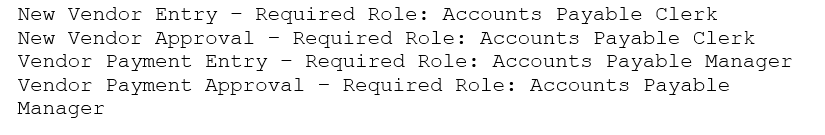
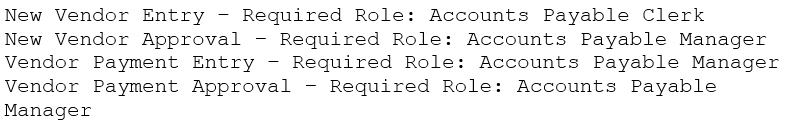
✑ New Vendor Entry `" Required Role: Accounts Payable Clerk
✑ New Vendor Approval `" Required Role: Accounts Payable Clerk
✑ Vendor Payment Entry `" Required Role: Accounts Payable Clerk
✑ Vendor Payment Approval `" Required Role: Accounts Payable Manager
Which of the following changes to the security configuration of the accounts payable module would BEST mitigate the risk?
A.
B.
C.
D.
The IT security department finds the following security configuration for the accounts payable module:
✑ New Vendor Entry `" Required Role: Accounts Payable Clerk
✑ New Vendor Approval `" Required Role: Accounts Payable Clerk
✑ Vendor Payment Entry `" Required Role: Accounts Payable Clerk
✑ Vendor Payment Approval `" Required Role: Accounts Payable Manager
Which of the following changes to the security configuration of the accounts payable module would BEST mitigate the risk?
A.
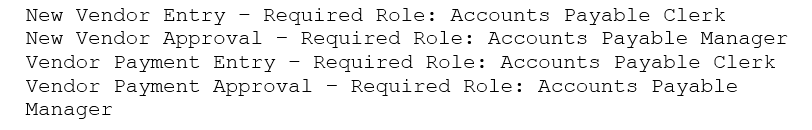
B.
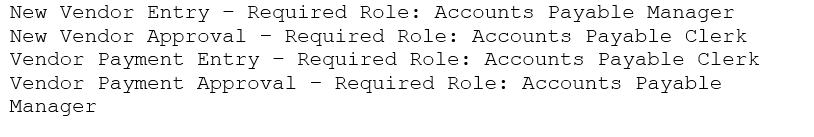
C.
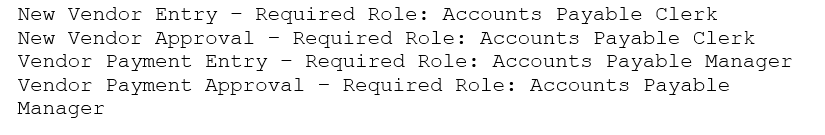
D.
send
light_mode
delete
All Pages
