CompTIA CAS-003 Exam Practice Questions (P. 5)
- Full Access (480 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
Question #41
A security engineer has implemented an internal user access review tool so service teams can baseline user accounts and group memberships. The tool is functional and popular among its initial set of onboarded teams. However, the tool has not been built to cater to a broader set of internal teams yet. The engineer has sought feedback from internal stakeholders, and a list of summarized requirements is as follows:
✑ The tool needs to be responsive so service teams can query it, and then perform an automated response action.
✑ The tool needs to be resilient to outages so service teams can perform the user access review at any point in time and meet their own SLAs.
✑ The tool will become the system-of-record for approval, reapproval, and removal life cycles of group memberships and must allow for data retrieval after failure.
Which of the following need specific attention to meet the requirements listed above? (Choose three.)
✑ The tool needs to be responsive so service teams can query it, and then perform an automated response action.
✑ The tool needs to be resilient to outages so service teams can perform the user access review at any point in time and meet their own SLAs.
✑ The tool will become the system-of-record for approval, reapproval, and removal life cycles of group memberships and must allow for data retrieval after failure.
Which of the following need specific attention to meet the requirements listed above? (Choose three.)
- AScalability
- BLatency
- CAvailability
- DUsability
- ERecoverability
- FMaintainability
Correct Answer:
BCE
BCE
send
light_mode
delete
Question #42
The board of a financial services company has requested that the senior security analyst acts as a cybersecurity advisor in order to comply with recent federal legislation. The analyst is required to give a report on current cybersecurity and threat trends in the financial services industry at the next board meeting. Which of the following would be the BEST methods to prepare this report? (Choose two.)
- AReview the CVE database for critical exploits over the past year
- BUse social media to contact industry analysts
- CUse intelligence gathered from the Internet relay chat channels
- DRequest information from security vendors and government agencies
- EPerform a penetration test of the competitor's network and share the results with the board
Correct Answer:
AD
AD
send
light_mode
delete
Question #43
The Chief Information Security Officer (CISO) has asked the security team to determine whether the organization is susceptible to a zero-day exploit utilized in the banking industry and whether attribution is possible. The CISO has asked what process would be utilized to gather the information, and then wants to apply signatureless controls to stop these kinds of attacks in the future. Which of the following are the MOST appropriate ordered steps to take to meet the CISO's request?
- A1. Perform the ongoing research of the best practices 2. Determine current vulnerabilities and threats 3. Apply Big Data techniques 4. Use antivirus control
- B1. Apply artificial intelligence algorithms for detection 2. Inform the CERT team 3. Research threat intelligence and potential adversaries 4. Utilize threat intelligence to apply Big Data techniques
- C1. Obtain the latest IOCs from the open source repositories 2. Perform a sweep across the network to identify positive matches 3. Sandbox any suspicious files 4. Notify the CERT team to apply a future proof threat model
- D1. Analyze the current threat intelligence 2. Utilize information sharing to obtain the latest industry IOCs 3. Perform a sweep across the network to identify positive matches 4. Apply machine learning algorithms
Correct Answer:
C
C
send
light_mode
delete
Question #44
A software development team is conducting functional and user acceptance testing of internally developed web applications using a COTS solution. For automated testing, the solution uses valid user credentials from the enterprise directory to authenticate to each application. The solution stores the username in plain text and the corresponding password as an encoded string in a script within a file, located on a globally accessible network share. The account credentials used belong to the development team lead. To reduce the risks associated with this scenario while minimizing disruption to ongoing testing, which of the following are the BEST actions to take? (Choose two.)
- ARestrict access to the network share by adding a group only for developers to the share's ACL
- BImplement a new COTS solution that does not use hard-coded credentials and integrates with directory services
- CObfuscate the username within the script file with encoding to prevent easy identification and the account used
- DProvision a new user account within the enterprise directory and enable its use for authentication to the target applications. Share the username and password with all developers for use in their individual scripts
- ERedesign the web applications to accept single-use, local account credentials for authentication
Correct Answer:
AB
AB
send
light_mode
delete
Question #45
A security consultant is attempting to discover if the company is utilizing databases on client machines to store the customer data. The consultant reviews the following information:
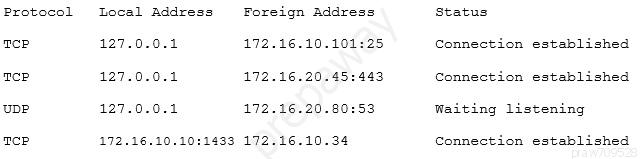
Which of the following commands would have provided this output?
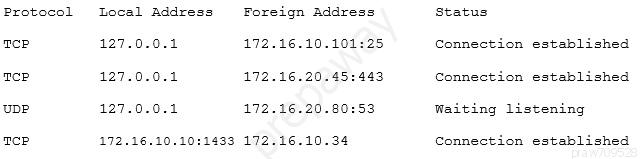
Which of the following commands would have provided this output?
send
light_mode
delete
Question #46
Management is reviewing the results of a recent risk assessment of the organization's policies and procedures. During the risk assessment it is determined that procedures associated with background checks have not been effectively implemented. In response to this risk, the organization elects to revise policies and procedures related to background checks and use a third-party to perform background checks on all new employees. Which of the following risk management strategies has the organization employed?
send
light_mode
delete
Question #47
A company wants to perform analysis of a tool that is suspected to contain a malicious payload. A forensic analyst is given the following snippet:
^32^[34fda19(fd^43gfd/home/user/lib/module.so.343jk^rfw(342fds43g
Which of the following did the analyst use to determine the location of the malicious payload?
^32^[34fda19(fd^43gfd/home/user/lib/module.so.343jk^rfw(342fds43g
Which of the following did the analyst use to determine the location of the malicious payload?
- ACode deduplicators
- BBinary reverse-engineering
- CFuzz testing
- DSecurity containers
Correct Answer:
B
B
send
light_mode
delete
Question #48
An advanced threat emulation engineer is conducting testing against a client's network. The engineer conducts the testing in as realistic a manner as possible.
Consequently, the engineer has been gradually ramping up the volume of attacks over a long period of time. Which of the following combinations of techniques would the engineer MOST likely use in this testing? (Choose three.)
Consequently, the engineer has been gradually ramping up the volume of attacks over a long period of time. Which of the following combinations of techniques would the engineer MOST likely use in this testing? (Choose three.)
- ABlack box testing
- BGray box testing
- CCode review
- DSocial engineering
- EVulnerability assessment
- FPivoting
- GSelf-assessment
- HWhite teaming
- IExternal auditing
Correct Answer:
AEF
AEF
send
light_mode
delete
Question #49
A security engineer must establish a method to assess compliance with company security policies as they apply to the unique configuration of individual endpoints, as well as to the shared configuration policies of common devices.
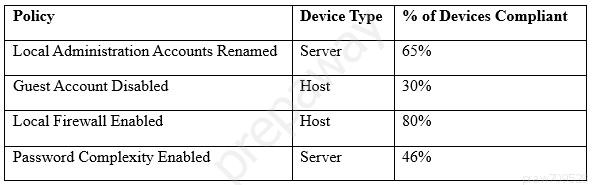
Which of the following tools is the security engineer using to produce the above output?
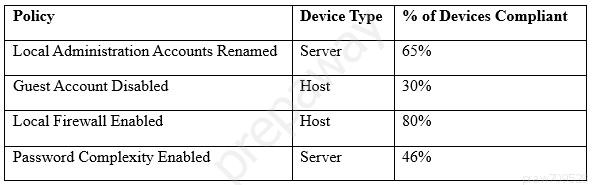
Which of the following tools is the security engineer using to produce the above output?
send
light_mode
delete
Question #50
A newly hired systems administrator is trying to connect a new and fully updated, but very customized, Android device to access corporate resources. However, the MDM enrollment process continually fails. The administrator asks a security team member to look into the issue. Which of the following is the MOST likely reason the MDM is not allowing enrollment?
- AThe OS version is not compatible
- BThe OEM is prohibited
- CThe device does not support FDE
- DThe device is rooted
Correct Answer:
D
D
send
light_mode
delete
All Pages
