Palo Alto Networks PCNSE Exam Practice Questions (P. 4)
- Full Access (619 questions)
- One Year of Premium Access
- Access to one million comments
- Seamless ChatGPT Integration
- Ability to download PDF files
- Anki Flashcard files for revision
- No Captcha & No AdSense
- Advanced Exam Configuration
Question #31
A session in the Traffic log is reporting the application as `incomplete.`
What does `incomplete` mean?
What does `incomplete` mean?
- AThe three-way TCP handshake was observed, but the application could not be identified.
- BThe three-way TCP handshake did not complete.Most Voted
- CThe traffic is coming across UDP, and the application could not be identified.
- DData was received but was instantly discarded because of a Deny policy was applied before App-ID could be applied.
Correct Answer:
B
B
 GPT
GPT
The designation `incomplete` in Palo Alto Network's Traffic logs specifically indicates that the three-way TCP handshake between devices was not successfully completed. This condition highlights a foundational communication failure, where essential TCP packets did not transmit in full, leading to unsuccessful session establishment. It’s crucial to understand that `incomplete` does not relate to post-handshake data transmission or application identification failures. Thus, monitoring these logs aids in identifying and troubleshooting preliminary connectivity issues within network operations.
send
light_mode
delete
Question #32
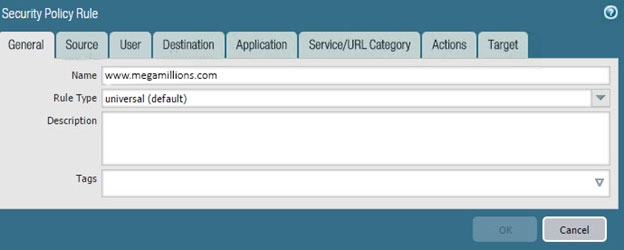
Refer to the exhibit.
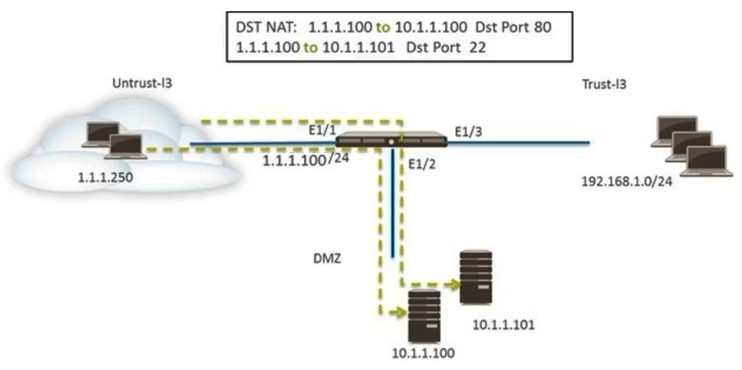
An administrator is using DNAT to map two servers to a single public IP address. Traffic will be steered to the specific server based on the application, where Host
A (10.1.1.100) receives HTTP traffic and Host B (10.1.1.101) receives SSH traffic.
Which two Security policy rules will accomplish this configuration? (Choose two.)
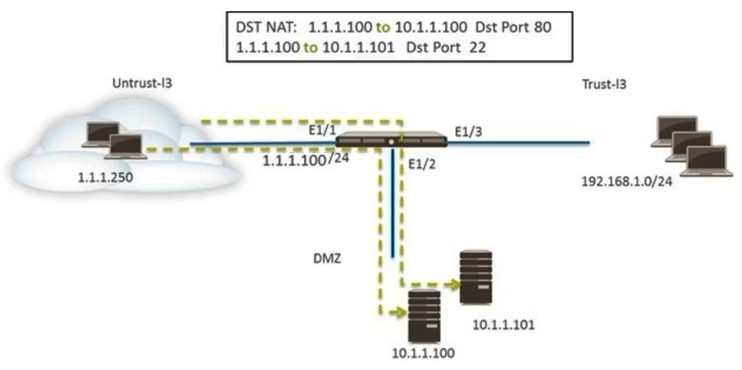
An administrator is using DNAT to map two servers to a single public IP address. Traffic will be steered to the specific server based on the application, where Host
A (10.1.1.100) receives HTTP traffic and Host B (10.1.1.101) receives SSH traffic.
Which two Security policy rules will accomplish this configuration? (Choose two.)
- AUntrust (Any) to Untrust (10.1.1.1), web-browsing ג€" Allow
- BUntrust (Any) to Untrust (10.1.1.1), ssh ג€" Allow
- CUntrust (Any) to DMZ (1.1.1.100), web-browsing ג€" AllowMost Voted
- DUntrust (Any) to DMZ (1.1.1.100), ssh ג€" AllowMost Voted
- EUntrust (Any) to DMZ (10.1.1.100, 10.1.1.101), ssh, web-browsing ג€" Allow
Correct Answer:
CD
CD
send
light_mode
delete
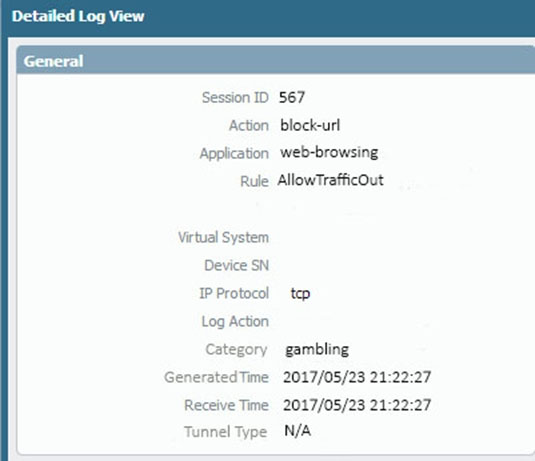
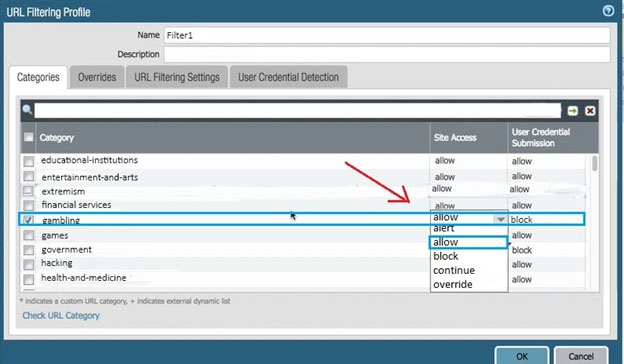
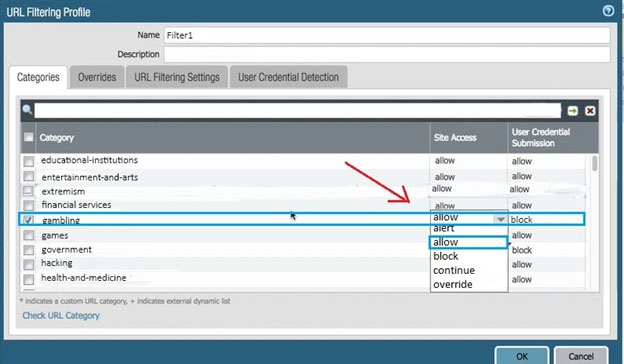
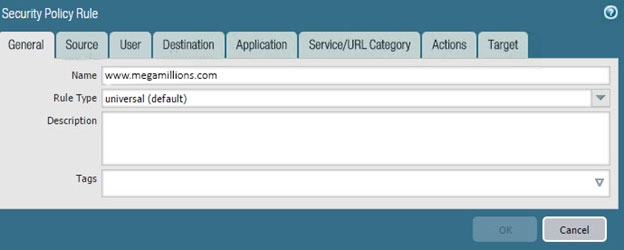
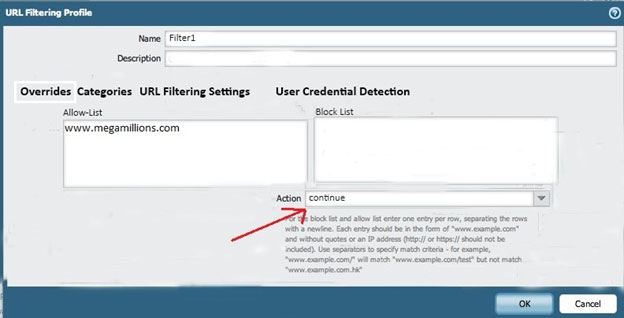
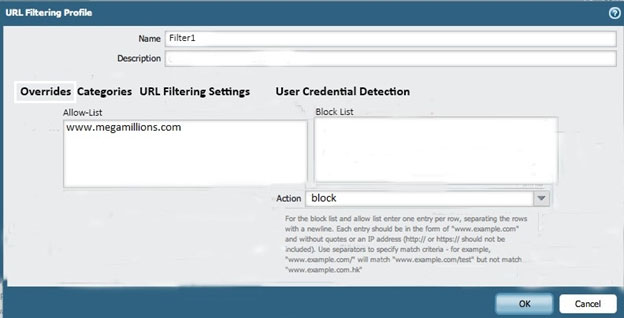
Question #33
An administrator needs to determine why users on the trust zone cannot reach certain websites. The only information available is shown on the following image.
Which configuration change should the administrator make?
A.
B.
C.
D.
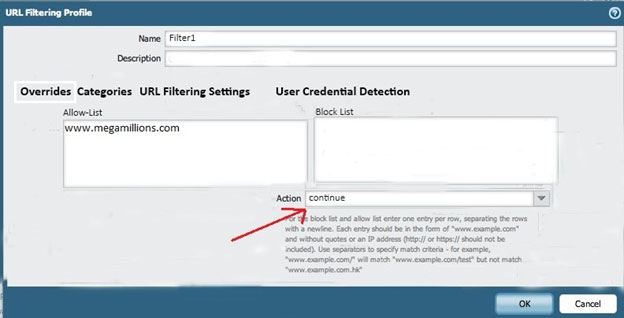
E.
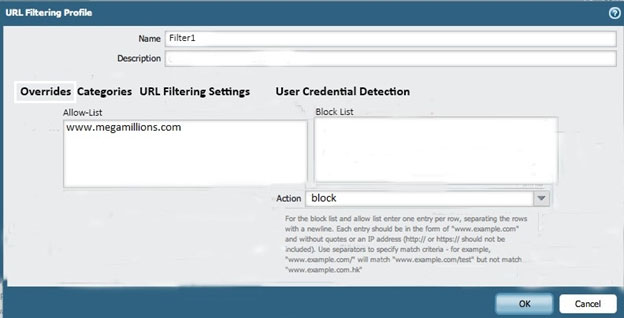
Which configuration change should the administrator make?
A.
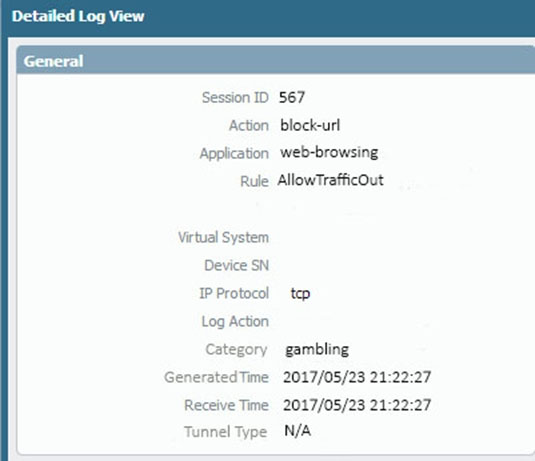
B.
C.
D.
E.
send
light_mode
delete
Question #34
Which three settings are defined within the Templates object of Panorama? (Choose three.)
- ASetupMost Voted
- BVirtual RoutersMost Voted
- CInterfacesMost Voted
- DSecurity
- EApplication Override
Correct Answer:
ABC
ABC
 GPT
GPT
Correct choices A, B, and C focus on network and device configurations. Specifically, Templates in Panorama allow for the centralized management of these settings, enabling the consistent deployment of configurations like "Setup," "Virtual Routers," and "Interfaces." Options D and E, relating to Security and Application Override respectively, fall under Device Group objects, which handle policy and object management instead.
send
light_mode
delete
Question #35
A customer has an application that is being identified as unknown-tcp for one of their custom PostgreSQL database connections.
Which two configuration options can be used to correctly categorize their custom database application? (Choose two.)
Which two configuration options can be used to correctly categorize their custom database application? (Choose two.)
- AApplication Override policy.Most Voted
- BSecurity policy to identify the custom application.
- CCustom application.Most Voted
- DCustom Service object.
Correct Answer:
AC
Reference:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clc6CAC
AC
Reference:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clc6CAC
send
light_mode
delete
Question #36
An administrator logs in to the Palo Alto Networks NGFW and reports that the WebUI is missing the Policies tab.
Which profile is the cause of the missing Policies tab?
Which profile is the cause of the missing Policies tab?
- AAdmin RoleMost Voted
- BWebUI
- CAuthentication
- DAuthorization
Correct Answer:
A
A
 GPT
GPT
The missing Policies tab in the Palo Alto Networks NGFW WebUI is directly related to the admin role configuration. If the appropriate permissions are not assigned within the admin role profile, certain tabs and options, like the Policies tab, will not be visible. This setup helps in customizing access and maintaining a secure and organized administration environment. Always ensure the admin roles are properly configured to grant necessary access rights to users.
send
light_mode
delete
Question #37
An administrator has left a firewall to use the default port for all management services.
Which three functions are performed by the dataplane? (Choose three.)
Which three functions are performed by the dataplane? (Choose three.)
- AWildFire updates
- BNATMost Voted
- CNTP
- DantivirusMost Voted
- Efile blockingMost Voted
Correct Answer:
BDE
BDE
 GPT
GPT
Exactly! Things like updates or NTP are indeed a part of what the control plane handles, not the dataplane. The dataplane's job is more about dealing with stuff that affects actual data packets as they come and go through the firewall. This includes functions like NAT, antivirus, and file blocking. This helps ensure efficient packet processing and relevant security checks without overloading the system with non-direct data handling tasks. So, remembering this distinction can be super crucial, especially when tweaking or troubleshooting firewall settings!
send
light_mode
delete
Question #38
An administrator is using Panorama and multiple Palo Alto Networks NGFWs. After upgrading all devices to the latest PAN-OSֲ® software, the administrator enables log forwarding from the firewalls to Panorama. Pre-existing logs from the firewalls are not appearing in Panorama.
Which action would enable the firewalls to send their pre-existing logs to Panorama?
Which action would enable the firewalls to send their pre-existing logs to Panorama?
- AUse the import option to pull logs into Panorama.
- BA CLI command will forward the pre-existing logs to Panorama.Most Voted
- CUse the ACC to consolidate pre-existing logs.
- DThe log database will need to exported form the firewalls and manually imported into Panorama.
Correct Answer:
B
B
send
light_mode
delete
Question #39
A firewall just submitted a file to WildFire for analysis. Assume a 5-minute window for analysis. The firewall is configured to check for verdicts every 5 minutes.
How quickly will the firewall receive back a verdict?
How quickly will the firewall receive back a verdict?
- AMore than 15 minutes
- B5 minutes
- C10 to 15 minutes
- D5 to 10 minutesMost Voted
Correct Answer:
D
D
send
light_mode
delete
Question #40
What are the differences between using a service versus using an application for Security Policy match?
- AUse of a ג€serviceג€ enables the firewall to take immediate action with the first observed packet based on port numbers. Use of an ג€applicationג€ allows the firewall to take immediate action if the port being used is a member of the application standard port list.
- BThere are no differences between ג€serviceג€ or ג€applicationג€. Use of an ג€applicationג€ simplifies configuration by allowing use of a friendly application name instead of port numbers.
- CUse of a ג€serviceג€ enables the firewall to take immediate action with the first observed packet based on port numbers. Use of an ג€applicationג€ allows the firewall to take action after enough packets allow for App-ID identification regardless of the ports being usedMost Voted
- DUse of a ג€serviceג€ enables the firewall to take action after enough packets allow for App-ID identification
Correct Answer:
C
Reference:
https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-admin/app-id/app-id-overview
C
Reference:
https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-admin/app-id/app-id-overview
send
light_mode
delete
All Pages
